Thank you for visiting nature.com. You are using a browser version with limited support for CSS. To obtain the best experience, we recommend you use a more up to date browser (or turn off compatibility mode in Internet Explorer). In the meantime, to ensure continued support, we are displaying the site without styles and JavaScript.
Advertisement
Scientific Reports volume 15, Article number: 9703 (2025)
Metrics details
The sensitive nature of the data processed by the critical infrastructures of a shared platform like the internet of things (IoT) makes it vulnerable to a wide range of security risks. These infrastructures must have robust security measures to protect the privacy of the user data transmitted to the processing systems that utilize them. However, data loss and complexities are significant issues when handling enormous data in IoT applications. This paper uses a reptile search optimization algorithm to offer attuned data protection with privacy scheme (ADP2S). This study follows the reptiles’ hunting behaviours to find a vulnerability in our IoT service’s security. The system activates the reptile swarm after successfully gaining access to explode ice. An attack of protection and authentication measures explodes at the breach location. The number of swarm densities and the extent to which they explore a new area are both functions of the severity of the breach. Service response and related loss prevention time verify fitness according to the service-level fitness value. The user and the service provider contribute to the authentication, which is carried out via elliptic curve cryptography and two-factor authentication. The reptile’s exploration and exploitation stages are merged by sharing a similar search location across the initialized candidates. The proposed scheme leverages breach detection and protection recommendations by 11.37% and 8.04%, respectively. It reduces the data loss, estimation time, and complexity by 6.58%, 10.9%, and 11.21%, respectively.
Data protection is an important task to perform in every application and system. Data protection secures the data presented in the database. The Internet of Things (IoT) is used for data protection, enhancing the systems’ efficiency and feasibility. IoT is mainly used here to improve communication and interaction processes1. IoT-based critical infrastructure is widely used in many applications. Specific data analyses and techniques are used for the data protection process. The significant elements of critical infrastructure are human, cyber, and physical2. Data protection ensures the safety and security of information stored in the database. IoT-based critical infrastructure provides critical information required to perform a particular task in an application3. Fundamental values and variables are detected from the database, which offers feasible data for further processes in critical infrastructure systems. The cyber security system is used to protect data from third-party members. Cyber security analysis generates important aspects and effects of the database that produce optimal data for government and public projects4.
Privacy-preserving policies and schemes are primarily used in various applications. The main goal of the privacy-preserving scheme is to ensure the safety and security of users’ data from unknown third-party members5. Privacy preservation in critical infrastructure is a crucial task. Various models and methods ensure the user’s privacy from attackers. A bi-level optimization model is used in critical infrastructure6. The actual aim of the optimization model is to detect the security issues that occur during specific tasks. Bi-level optimization model maximizes accuracy in the problem-detection process. Bi-level optimization model improves users’ privacy and security range in critical infrastructure7. Cryptographic encryption techniques are also used in critical infrastructure. A privacy-preserving strategy is used in encryption that enhances the necessary infrastructure security level8. Important fundamental values and features are secured in the database, reducing overall data loss in critical infrastructure. A wireless sensor network (WSN) is used for security protection in essential infrastructure systems9. WSN monitors the information using wireless sensors that improve reliability and ensure the safety of users’ privacy from attackers. WSN increases users’ personal information’s safety and security levels10.
Optimization methods and techniques are used for critical infrastructure security systems. The main aim of the optimization method is to improve the robustness and security range in critical infrastructure11. A novel heuristic simulation optimization method is most widely used for critical infrastructure security systems. The optimization method identifies the datasets required to perform a particular task in an application. The optimization method reduces the computation cost and time consumption ratio, which enhances the user’s data from the attackers12. The optimization method improves the overall quality of service (QoS) range in critical infrastructure and reduces the complexity level in computation processes. The genetic algorithm-based optimization method is also used for essential infrastructure13. The genetic algorithm identifies the key values presented in the user’s details. The genetic algorithm ensures the safety of fundamental values, improving critical infrastructure’s performance and feasibility ratio. A mathematical optimization model is also implemented for critical infrastructure security. The mathematical optimization model detects the features and patterns of security management systems14,15. The key contribution of the research article is given as follows:
Introduction of a novel ADP2S scheme utilizing reptile search optimization for enhanced data protection in critical infrastructures.
Implementing advanced security measures such as elliptic curve cryptography and two-factor authentication strengthens the authentication process.
Development of a comprehensive system to detect and respond to security breaches, thereby preventing data loss in IoT applications.
The organization subsection of the manuscript is arranged in the following order: “Related works” section is an introduction, related works, followed by the objective of the study; “The proposed scheme” section discusses the proposed ADP2S scheme; “The proposed scheme” section discusses the sequential resource allocation; “Results and implications” section is results and discussion includes the performance comparison using various metrics, “Compute new privacy measure such that” section concludes the research summary.
Hao et al.16 proposed a distributed anomaly detection-based resource allocation for industrial cyber-physical systems (ICPS). The traffic and anomalies are detected using a distributed detection method that provides feasible data for the allocation process. Optimization problems are solved based on specific functions and conditions. The detected distributed anomaly reduces the error ratio in the resource allocation process. The proposed method maximizes the accuracy in resource allocation, which enhances the performance and efficiency range of ICPS.
Chinnasamy et al.17 proposed the Blockchain 6G-Based Wireless Network Security Management with Optimization Using Machine Learning Techniques. This study implements a blockchain-based user datagram transit protocol incorporating reinforcement projection regression to manage the security of 6G wireless sensor networks. After that, the author used artificial democratic cuckoo glowworm remora optimization to finish optimizing the network. Several network characteristics, including energy efficiency, packet delivery ratio, accuracy, end-to-end latency, and throughput, have generated the simulation results. It can determine which node and route are best for data transmission to reduce network traffic. The suggested method achieved a throughput of 97%, energy efficiency of 95%, accuracy of 96%, end-to-end latency of 50%, and packet delivery ratio of 94%.
Oliva et al.18 introduced a multi-criteria model for security assessment in large infrastructure construction sites. The actual goal of the presented model is to select feasible construction for the sites. Specific criteria are used in the multi-criteria model, which provides relevant data for site selection and construction processes. The risks, attacks, and challenges are also detected, which reduces the overall damage range in large infrastructure sites. Experimental results show that the introduced model enhances the performance and accuracy of critical infrastructure systems.
Dong et al.19 developed an integrated infrastructure plan analysis for a resilience scorecard. Infrastructure vulnerability and risks are identified by analysis that provides feasible data for further processes. The proposed study mainly addresses road infrastructure vulnerabilities to access critical facilities. An integrated infrastructure analysis process reduces the identified gaps and latency. The proposed analysis method improves resilience and infrastructure’s overall efficiency and reliability.
Silva et al.20 presented a new Privacy Risk Assessment (PRA) and Privacy-Preserving Monitoring(PPM). Natural language processing tools are used here to address an application’s risks and privacy issues. Data transaction-based threats and attacks occur during the transaction and further processes. Compared with other methods, the proposed method achieves high accuracy in privacy-preserving policies, increasing the security of the systems.
Wang et al.21 introduced a deep learning (DL) based resilience analysis framework for critical infrastructure systems. DL is mainly used here to identify the attributes and variables with vulnerabilities in infrastructure systems. Failure propagation is also used here to detect the problems presented in the computation and identification processes. DL technique improves the accuracy of strategies, enhancing the systems’ performance and effectiveness range. The introduced framework ensures the security and safety levels in critical infrastructure systems.
Rios et al.22 designed a security level agreement (SLA) for Internet of Things (IoT) platforms and applications. The main aim of the proposed method is to increase users’ security and privacy ratio in IoT platforms. The proposed method is also used in cloud-based IoT platforms. The exact relationship among components and variables is detected by SLA, which provides feasible data for security management systems. Experimental results show that the proposed SLA maximizes safety and improves the efficiency and significance range of IoT networks. Feizollahibarough et al.23 developed a security-aware virtual machine for decision-making processes. The virtual machine is mainly used here to address the resources required to make a particular decision in an application. Security-aware frameworks identify the cumulative vulnerability ratio of the physical machine. The recognized framework provides optimal information for decision-making processes. The introduced frameworks achieve high accuracy in decision-making, improving the systems’ feasibility and robustness.
Bing et al.24 presented a meta-learning framework based on a memory-augmented neural network (M-ANN) for critical infrastructure systems. M-ANN detects the valuable data and variables from the database that provide necessary information for further processes. M-ANN also improves the accuracy ratio in resource allocation and scheduling processes. The proposed framework enhances critical infrastructure systems’ performance and efficiency range compared to other frameworks.
Authors in25 recommended the Intelligent Breach Detection System into 6G Enabled Smart Grid-Based Cyber-Physical Systems (SGCPS). The review covers various topics, such as intrusion detection systems enabled by artificial intelligence, methods for detecting False Data Injection (FDI) attacks, intrusion detection systems based on anomalies, and adaptive robust state estimators. It concludes with introducing a new intrusion detection model called the AI-IBDS, which uses the Grey Wolf Algorithm and Artificial Neural Networks (GWAANN) to achieve optimized detection of network intrusions in energy systems. Extensive analysis and comparison of performance metrics show that the proposed GWAANN method outperforms traditional classification methods like SVM and KNN in detecting critical events and improving cybersecurity measures. This highlights the potential of AI-driven intrusion detection technologies to strengthen network security and resilience in SGCPS environments, leading to safer and more efficient energy distribution networks in the digital age.
Brignoli et al.26 proposed a distributed security framework for ICT infrastructures. The proposed framework predicts the network threats that are presented in an infrastructure. The distributed framework provides feasible solutions to the threats that reduce the latency in performing specific tasks. Cyber security indicators are also used here to detect problems and threats from an infrastructure design. The proposed framework maximizes the safety and security level in ICT infrastructures.
Bringhenti et al.27 designed a novel methodology for the software-defined network (SDN) aware Internet of Things (IoT) networks. Maximum satisfiability modulo theories are used here to provide adequate data for allocation and scheduling processes. The proposed method detects the exact attacks that occurred in SDN systems and offers the optimal solution to solve the attacks. The proposed method enhances IoT networks’ performance and feasibility ratio compared with other methods.
Miloslavskaya et al.28 developed a security zone infrastructure for network security intelligence centres (NSIC). The main aim of the proposed framework is to detect the advanced threats presented in NSIC. Specific functions and schemes are used here to identify the exact cause of threats in NSIC. The proposed framework provides fewer attack services to users, which maximizes the efficiency of NSIC. The introduced framework ensures the safety and security of data presented in NSIC.
In their study, Javanmardi et al.29 tackle the emerging difficulties in Software-Defined Networking (SDN)-based Internet of Things (IoT)-Fog networks by introducing a new method called Secure Workflow Scheduling, abbreviated as S-FoS. The paper addresses the issue of enhancing performance in these networks, with a particular focus on the importance of incorporating security measures into workflow scheduling. The main goal is to develop a robust scheduling method to improve the overall effectiveness of SDN-based IoT-Fog networks. The authors utilize pioneering techniques to accomplish this objective by incorporating security considerations into the workflow scheduling process. Their research demonstrates that the S-FoS technique effectively enhances performance while maintaining a solid security foundation. Nevertheless, the literature review recognizes specific constraints, providing insight into areas that require additional investigation and improvement to enhance the practicality and extent of the suggested approach.
Chinnasamy et al.30 suggested the Ciphertext-Policy Attribute-Based Encryption (CP-ABE) for Cloud Storage. There is a risk that user and data privacy might be compromised due to the access policy being delivered as plaintext in the current CP-ABE system instead of an encrypted version. This issue is addressed by the author’s novel method, which employs a signature verification approach to prevent insider assaults and a hashing algorithm to conceal the access policy. From a computational and expressive policy perspective, the suggested system is contrasted with current CP-ABE methods. The author may check how well any possible IoT access control system works. The proposed study further analyzes security against attacks with indistinguishable adaptive selected ciphertext.
Widel et al.31 designed a meta-attack language framework and attack graph-based countermeasure selection. The main aim of the proposed framework is to ensure the safety and security of critical infrastructure. An attack graph is used here to predict the attacks presented in infrastructure. The attack language framework detects the optimal set of countermeasures. The proposed frameworks reduce computation time and computational cost, improving the systems’ flexibility and scalability.
Dedousis et al.32 introduced a security-aware framework for industrial engineering processes. The main aim of the proposed framework is to identify crucial flows and components and to classify the types of physical systems. The proposed framework is widely used for designing processes that reduce both time and energy consumption range in the computation process. The introduced frameworks increase industrial engineering systems’ overall security and feasibility levels.
Table 1 gives a comparative summary of the existing related works.
Under the adaptive hunting behaviour, multi-modal threat detection, and low computational overhead, the Reptile Swarm Optimization (RSO) algorithm outshines other swarm-based and AI-driven optimization techniques like Particle Swarm Optimization (PSO), Genetic Algorithm (GA), or Deep Learning (DL) when it comes to optimizing for IoT security. With its exploration–exploitation balance, RSO can monitor and eradicate changing cyber risks in real time, unlike PSO’s premature convergence problem in dynamic IoT contexts. RSO is the way for time-sensitive security applications like intrusion detection and anomaly prediction in IoT networks since it uses reptile-inspired quick decision-making, unlike GA, which depends on mutation and crossover processes, which may cause delays. To add insult to injury, despite their outstanding accuracy, resource-constrained IoT nodes cannot handle the computational rigour and massive labelled datasets needed by Deep Learning-based security models. In contrast, RSO improves intrusion response strategies, optimizes cryptographic key management, and reacts to real-time network variations using few computing resources. Security for critical infrastructures powered by the Internet of Things (IoT) may be improved using RSO’s scalable, efficient, and resilient multi-agent intelligence, decentralized decision-making, and adaptive swarm coordination solutions.
The design goal of ADP2S using data protection and security measures in critical infrastructure is improved based on the user requests and responses from the IoT environment. Users’ input is observed through AI and IoT requests and responses.
For IoT applications, the primary aim of the suggested framework is to reinforce data protection and security protocols in critical infrastructure. Reptile search and AI-assisted devices optimize real-time intrusion and vulnerability detection. Distributed user information secured through high security ensures secure data management in IoT environments and better data control to protect privacy. The proposed approach includes two-factor authentication, demand from consumers analysis, sequential resource allocation, and service-level fitness estimation. The collaboration of these elements guarantees the protection and confidentiality of user information on the IoT platform. The strategy authenticates users, measures service-level fitness, and efficiently allocates resources using mathematical methods and optimization algorithms. These algorithms efficiently reduce breaches and vulnerabilities. Elliptic curve cryptography and two-factor authentication are used for data security and privacy. These controls prevent unauthorized involvement with the system and protect sensitive data.
The AI-assisted devices are used to process systems and applications in real-time. Reptile search optimization is aided in identifying breaches in critical infrastructure with appropriate request processing, which relies on distributed user information with high-level security. Data protection in critical infrastructure provides more control for the individual’s information and monitors who can access it. The user-distributed information in IoT is converted into a request to ensure privacy. In this request processing, the reptile search optimization algorithm efficiently addresses the breach and theft in that environment. The input user requests are processed to exchange services between the IoT platform and the available resources for sensitive data handling. In this proposed scheme, the addressing of adversaries or breaches in services is considered to augment the exploration and fitness of the service connection.
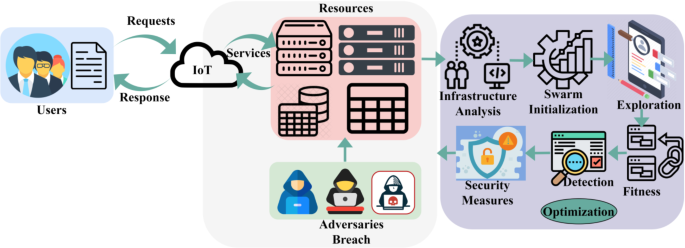
The proposed scheme considers many adversaries and threats, such as unauthorized access, intrusions of data security, and privacy violations. It presupposes malicious actors may exploit system vulnerabilities to obtain unauthorized access to confidential data. Confidentiality, availability, and integrity of user data are the principal security objectives of the proposed scheme. By employing robust authentication techniques, methods of encryption, and access control policies, it intends to accomplish these objectives. The proposed scheme is portrayed in Fig. 1.
Proposed scheme.
The user requesting services are processed using ADP2S to control high-security risks due to handling information, whereas the position and location of the breach in resources are identified. The sophisticated IoT is used to handle user requests and responses and process multiple services, which serves as different types of moments for the position or location of the breach being identified in critical infrastructure, which is unavailable.
The requests and responses from the IoT platform are analyzed to provide services and identify the breach in a user connecting IoT service due to handling highly secured information. The objective of this attuned data protection with a privacy scheme used for reptile search optimization is to mitigate the breach position and ensure the sensitive information in the IoT platform. The scheme is designed to increase data protection and privacy measures in AI-based applications through swarm initialization. The processing system in this article is a combination of software and hardware components that can grasp and analyze user requests with high security to ensure privacy on that platform. The request is observed from users through AI-assisted devices or sensors in critical infrastructure and reduces adversaries and vulnerabilities under controlled processing time. Therefore, balancing requests and responses for processing appropriate services in the IoT platform for different moments, like reptile behaviour, is analyzed. Critical infrastructures reliant on the Internet of Things (IoT) are better protected from cyberattacks, according to the security analysis results of the proposed ADP2S. To detect and eliminate threats such as data breaches, denial-of-service (DoS) assaults, and unauthorized access in real time, ADP2S uses swarm intelligence inspired by reptiles. The explode ice mechanism is implemented to counterattack and strengthen the system’s resistance automatically. Further, the approach ensures that data is secret and protected from malicious manipulations by prioritizing privacy preservation via encryption and safe authentication procedures. By constantly adjusting to new security threats, ADP2S improves network availability and integrity and stops interruptions in their tracks. One dependable solution for smart grids, healthcare IoT, industrial control systems, and intelligent transportation networks is ADP2S, which greatly improves the security posture of IoT-driven infrastructures through adaptive defence mechanisms, proactive monitoring, and automated response strategies. The first user requests input (({U}_{rq})) is observed through wireless sensors or devices and is expressed as
where,
where the variables (DP, {U}_{rq}, {U}_{rs}) and (T) used to represent sensitive data processing for (N) users based on requests (rq) and responses (rs). The processing systems analyze (i) services at (T) intervals in the IoT platform. If the variables ({S}_{C}) and ({R}_{e}) denotes service connections and resource allocation for storing and collecting user information. Based on the instance, the second user request is processed with ({s}_{d}),({B}_{p}) and ({EX}_{P}) swarm density, breach position, and location exploration are identified through reptile swarm optimization (RSO). The third objective is to minimize the adversaries and vulnerabilities in processing services with the condition (DP{left({U}_{rq}right)}_{i} forall Nin {B}_{p}). Where,(U=left{text{1,2},dots , Uright}) illustrates a set of users in an IoT platform, then the number of service connections between resources and the IoT environment is addressed for distributing the user information to those resources at processing time (pt). The infrastructure analysis based on ({U}_{rq}times pt,) whereas the swarm initialization is ({U}_{rq}times { s}_{d}). From the overall service connection for processing and distributing the information in IoT using the constraints ({U}_{rq}times pt) and ({U}_{rq}times { s}_{d}) is the admittable service for addressing breaches/adversaries. The initialization process for ({S}_{C}) is presented in Fig. 2.
Initialization of ({S}_{C}).
The ({U}_{rq} in) the set (U) is disintegrated through (N) for exploration. In the first population initialization, (E{X}_{1} to E{X}_{P}) is generated considering unique reptile swarms. However, the initialized swarm is reused based on (E{X}_{P}) status. If the status is idle, then ({U}_{rq}) is allocated else ({U}_{rs}) is pursued through repeated iterations. A change observed in the service fitness disturbs this allocation wherein (Pin EX) is modified with new swarms (Fig. 2). Resource allocation in the IoT platform for service connection and infrastructure analysis is optimal in identifying the breach intensity and location using service-level fitness computations in the upcoming connections. In this sequence, the reptile swarm optimization is initialized in post-service access, which is essential for the user connecting IoT service to identify the breach and theft in that common platform for processing additional services. In infrastructure analysis, the swarm density changes based on the identified breach intensity in IoT services, and the location exploration is performed to ensure security is considered for maximum user request processing with high-level security. Further, the hunting patterns of the reptiles are used to identify the breach/adversaries at a similar time when information is distributed to the available resources. The service-level fitness computation uses the public service response and associated processing time. In particular, the service connection of available user information for controlling breaches and theft is the improving factor in this infrastructure analysis. For instance, location exploration is the prevailing sequence for service connection and resource allocation. The process of services in an IoT platform with associated user requests is analyzed for breach occurrence, which is essential in this proposed scheme.
In this sequential resource allocation for processing systems in the IoT platform, the user data distribution ({U}_{rq}times pt) for all the end-users accessing the particular application based on swarm flood ({s}_{d}) is the addressing breach occurrence. Instead, the pursuing user requests are analyzed with high security. Therefore, the probability of resource allocation for available service connection (left({rho }_{{S}_{C}}right)) processed continuously is given as
where,
Equations (4) and (5) compute the sequential service connection between the users and the IoT platform with an idle probability of identifying the breach. Hence, no more data distribution occurs in those resources, and then infrastructure analysis is performed using the above Eq. (5). Now, the resource allocation for further location analysis ({rho }_{{S}_{C}}) is expressed as
In Eq. (6), the resource allocation for initializing the reptile swarm is analyzed for user privacy, and it is valid for ({U}_{rq}times pt) and ({U}_{rq}times { s}_{d}) ensuring security in critical infrastructure. The processing systems in this crucial infrastructure provide service connection between the end-users in that IoT platform for mitigating breaches and adversaries using the condition ({U}_{rq}times pt) and ({U}_{rq}times { s}_{d}) is computed. The allocation using the initial population of ({S}_{d}) is presented in Fig. 3. The allocation using ({S}_{d}) is performed based on ({S}_{c}) achieved from ({U}_{req}). This allocation is performed in (EX) space (forall P) as ({U}_{rs}) generation. Throughout the response process, the allocated (P) is analyzed (forall T). In this (T), the ({S}_{c}) is alternatively computed.
Allocation using ({S}_{d}).
This computation is required for fitness validation such that (T) generates ({S}_{C}) is required for new ({S}_{d}) initialization (Fig. 3). The resource allocation for connecting services is descriptive using RSA. Therefore, the current user request conditions in ({U}_{rq}>pt) and ({rho }_{{EX}_{P}}), the occurred breach or vulnerabilities identified using fitness estimation is less than enough to satisfy Eq. (1). Similarly, the location exploration output prolongs service access across the IoT platform, hence, the associated time output in service disconnections and failures.
This computation is performed to identify breaches for position and location. The service disconnection indicates a breach occurrence in that platform. Therefore, the user data distribution to the processing systems using this infrastructure is analyzed and monitored to identify breaches when information exchange is time-invariant. Along with the idle time for service connection (service-level fitness) for (N) user request, the service disconnection in critical infrastructure is the identifying breach in this proposed scheme. The probability of service-level fitness (left({rho }_{{S}_{F}}right)) is computed as
where the variable (SRleft(rsright)) represents service response for validating the fitness and its associated time of service connection at (T) intervals. The reptile swarm is initialized to analyze the different types of moments in IoT for location exploration using service-level fitness size computed for all user requests to address breaches. Resource allocation for data protection and privacy measures in this infrastructure requires a high amount of associated time, thereby increasing the losses in IoT. Figure 4 presents the fitness estimation flow. The fitness estimation is performed using (EX forall 1 to P) such that the computation is increased. Considering the ({rho }_{SF} forall) it’s a maximum value (1),, the possible combination generates (SR(rs)). The remaining (P) is used as reallocating agents that generate new (E{X}_{P}) for ({S}_{D}). If ({S}_{C}ne P), then (DP) is reinitiated from ({rho }_{E{X}_{P}}); this is optimal for ({S}_{d}) such that (E{X}_{P}={R}_{e}times T) is achievable. Therefore, the iterations are recurrent for the validating (T) across new ({rho }_{SF}) (Refer to Fig. 4).
Fitness estimation flow.
The security measure for user privacy and data protection across the critical infrastructure is analyzed based on the constraint ({U}_{rq}>pt) and (Nleft(Uright)) for identifying losses, service disconnections, and associated time in that IoT platform. The swarm density variations are identifiable for breach detection using RSA to mitigate and authenticate the procedure through rational two-factor authentication. The following section represents the authentication processing for user privacy and data protection.
The secure information exchange and processing output in optimal service connection and resource allocation within this infrastructure using RSA is to mitigate the breach and adversaries in processing systems. From this instance, the preventive and confronting security for data protection and user privacy follows some security measures to avoid breaches and vulnerability in data processing. The authentication for the user and service provider relies on (({U}_{rq},{s}_{d},{S}_{F})) is the serving input for fitness evaluation to improve privacy measures. If the location exploration is identified, it indicates loss and breach in user information, and then new security measures are generated to ensure privacy. This authentication uses elliptic curve cryptography to administer the current processing systems based on sequential data analysis.
The Reptile Search Optimization method was developed to streamline the search process and increase the efficiency of finding breaches in critical infrastructure. To demonstrate the efficacy of this method in identifying potential security risks, mathematical demonstrations and simulations can be utilized to examine the robustness of this technique. The concept uses two-factor authentication and elliptic curve cryptography to secure sensitive data and user privacy. Elliptic curve cryptography is notable for its robustness against many cryptographic assaults, notably brute-force and key-compromising attacks. By utilizing this technique, the system can accomplish robust authentication, which makes it resistant to efforts to get access without authorization. To circumvent the authentication method, adversaries must simultaneously change many parameters, making it substantially more difficult to achieve their goal. The risk of successful assaults targeted at breaching user privacy or data protection measures is decreased when the system maintains a steady security posture to prevent such attacks.
In this authentication requires for enhancing data protection and user privacy in critical infrastructure between the successive service connections and fitness values, the following steps are to generate new privacy measures:
1. Let the variables (m) and (n) follow user request and response such that (mne n) for all data protection is provided based on different expectations and exploration.
2. Validate
3. Estimate the authentication
4. The reptile exploration and exploitation are combined for the current hunting patterns (Z) using a common search location from the initialized candidates such that ({S}_{F}<Z<{U}_{rq}left({s}_{d}right)), it is repeated for further request and response processing.
5. Compute new privacy measure ({N}_{PM}) such that
User privacy ensures authentication for service connection, and resource allocation relies on user and service provider performance to reduce breaches. The current hunting pattern of the reptiles is used for candidate initialization in the upcoming resource allocation to improve user privacy and data protection. The reptile exploration and exploitation are jointly computed for breach detection and data protection recommendations at different intervals, preventing losses. This authentication for processing systems in critical infrastructure uses RSA to identify changes in swarm density, thereby reducing breaches and threats and improving privacy measures. Here, the user information process relies on associated time intervals and losses in service-level fitness to identify location exploration. The security implementation process is illustrated in Fig. 5. The (SR left(rsright)) is generated for (min {U}_{rq}) and (nin {U}_{rs}) throughout the authentication process. Considering the ((m-1)times n) and (left(n-1right)times m) across ({N}_{{P}_{M}}Zequiv 1), the authentication response is analyzed. If the condition is not satisfied, then a new (left(m+1right)) and (left(n+1right)forall {S}_{F}=left(n+1right)left(m+1right)) is verified. This verification is required to prevent authentication failures across multiple n∀m (Fig. 5). Therefore, the security measures and data protection are authenticated together with two-factor authentication of data protection recommendation for the user and service provider for secure information access. Hence, the privacy measures remain stable for all swarm initialization.
Security implementation process.
The consecutive service connections and disconnections in critical infrastructure rely on fitness level and breach detection validation to modify security measures for breach position and location in available resources. Based on the sequence, the continuous sensor data processing is performed in an IoT platform with high security, and then the breaches and thefts are identified through ADP2S with the condition ({U}_{rq}>pt) and (Nleft(Uright)) is used to halt the breach service connection and prevent losses. Data breaches, losses, and thefts in the processing system are identified, and security measures are provided to protect the user information with high-level security at different intervals on the IoT platform. The security measures in critical infrastructure for user privacy and data protection using two-factor authentication for the user and service providers in both request and response processing instances.
The optimization approach for data protection and user privacy is analyzed through a series of access in 10 intervals. The total access demanded is 160, and the split gives 16 / intervals. First, the initialization is performed with 16 agents to connect 11 resources. Creating and utilizing a custom dataset in this research occurs in an organization considered a Data collection method that involves defining critical parameters such as intervals, total access needs, and agent-resource relationships. The custom dataset is created. Randomness in dataset development simulates stochasticity in real life to reproduce access requests across time and capture agent-resource interactions. The dataset size involves the total demand for access as 160 with the segment of 16 demands per interval for 16 agents along with the connected 11 resources. Each interval in an organization’s customized dataset is rigorously documented to capture system status and agent-resource connections. Validation is necessary to ensure the custom dataset’s accuracy and reliability. The custom dataset underpins data protection and user privacy optimization. It lets researchers assess how well the suggested approach improves critical infrastructure security. To create a simulation or custom dataset using the optimization approach discussed, one must carefully plan and generate data with great attention to detail. The simulation defines critical parameters, such as intervals, total access needs, and agent-resource relationships. Subsequently, artificial data is produced to replicate access requests over specific periods and to capture the process of agents establishing connections with resources. Randomness can be introduced to simulate stochastic aspects seen in the real world. Each interval is meticulously documented, capturing the system’s status and the linkages between the agent and resources. Certain properties, such as time intervals, access demands, and pertinent factors, are established when creating a custom dataset. The dataset is thereafter created, guaranteeing authenticity by considering resource limitations and possible clashes. Validation, privacy concerns, documentation, and potential collaboration are crucial elements of an all-encompassing procedure.
The initialization is performed based on ({U}_{rq} forall T) such that the iterations are repeated if ({S}_{d}>E{X}_{P}). This is therefore identified for two different combinations (i.e.) (EX times {rho }_{{S}_{c}}=1) and ({rho }_{{S}_{c}}*frac{n}{m}=1). From the two different combinations, the iterations are determined; the (left(m+1right)<n) condition is verified. If the condition is true, then the new allocation from 1 to (left(m-nright)) is performed using (P). It is to be noted that (P) is re-utilized from the previous ({S}_{d}) (Fig. 6). the search space (resource validation) is examined after the initialization process. This examination relies on (N) resources available, augmenting (N{C}_{P}) combination for different iterations. In this process, if a common (Pin {S}_{d}) visits a common resource, then the probability (i.e.) ({rho }_{{S}_{C}}) is either incremental/ decremental. This analysis is presented in Fig. 7.
Initialization process.
({rho }_{{S}_{c}}) and (P) analyses.
The proposed scheme is vibrant depending on the iterations for stabilizing ({rho }_{{S}_{C}}) and (P) requirement. Depending on the available (EX), the ({S}_{F}) is planned for the different intervals to be utilized. Considering the availability and (left(m+1right)<n) condition satisfaction, the new allocation is performed. This new allocation is validated for different (T) and ({rho }_{{S}_{F}}) conditions. The ({rho }_{{S}_{F}}=1 (max)) and ({rho }_{{S}_{F}}ne One) is concurrent if ({R}_{e}) is parallel. Therefore, if a joint agent is reassigned, then ({rho }_{Sp}=1) is retained. Contrarily, if no agent is reassigned, then ({rho }_{SP}=1) is retained. Contrarily, if no agents are available, then (P) fails (the downside in the above analysis), relating it to the decremental factor (Fig. 7). From this analysis, the ({N}_{PM}) level in both conditions is satisfied based on the previous (T). This analysis is presented in Fig. 8.
({N}_{PM}) and (SRleft(rsright)) analyses.
The analysis for ({N}_{PM}) over the varying (m=n) and (left(m+1right)<n) conditions are analyzed in Fig. 8. The ({rho }_{{S}_{F}}) increases the chance for (m=n) improvement such that authentication provisioning is maximized. Depending on the available (T), the allocations are performed; the ({N}_{PM}) reduction requires a new swarm agent. If a joint swarm agent is replicated, then (SRleft(rsright)) increases in due (T). This maximizes the ({N}_{PM}) for which iterations are mandatory. Across the new (EX), the (P) implications are random and therefore, unique exploration with new fitness is performed (Fig. 8). To minimize system compromise, breach detection should be prioritized. Identifying and limiting unauthorized access or cyber intrusions in real-time is important. Next, authentication is critical for limiting the possibility of illegal access to IoT networks by confirming that only authorized people and devices may connect. Once secured access is in place, encryption is crucial for keeping data private since it prevents access to sensitive information regardless of interceptions. Since IoT networks handle massive volumes of operational and personal data, ensuring privacy is a close second. This is because these networks must comply with legislation and maintain user confidence. Next, optimizing resource allocation is important to balance security enforcement with device constraints. This will minimize excessive computational overhead and preserve system efficiency. As a last point, service-level fitness may be achieved by ensuring security measures don’t slow down the system. This way, IoT networks can keep working perfectly while being well protected.
Using a swarm intelligence technique modelled after reptiles, the Attuned Data Protection with Privacy Scheme (ADP2S) aims to detect and mitigate security vulnerabilities in critical infrastructures that rely on the Internet of Things (IoT). Illegitimate access, data breaches, adversarial assaults, and denial-of-service (DoS) threats are all factors that might be accounted for in the threat model. When abnormalities are detected, the system triggers a reptile swarm mechanism, which uses hunting techniques similar to reptiles to find and reveal security vulnerabilities. Explode ice is an automatic countermeasure that blocks attack attempts and eliminates threats in real-time. It is activated when a vulnerability is detected. The adaptive security, real-time monitoring, and quick reaction offered by ADP2S’s proactive defensive mechanism make it an impervious solution to safeguard critical data and preserve infrastructure integrity.
The metrics of breach detection, protection recommendation, data loss, estimation time, and complexity are used for validating the proposed ADP2S. The service access and search solutions are varied according to the methods ICPS18, PRA-PPM20, M-ANN24, SVMPS23, and DMS26 along the proposed scheme. Table 2 shows the simulation environment.
In Fig. 9, the data protection and user privacy in critical infrastructures for improving the breach detection with ADP2S using a reptile search optimization algorithm rely on the available resource allocation and service connection. High-level security is provided for the user information distributed to the processing systems in these infrastructures, and it is analyzed through swarm initialization. In the user connection, IoT services are processed for all the user requests. The fitness is estimated using service response with the breach intensity, which helps to identify the breach position and location aided by RSA.
Breach detection.
The observed input request is analyzed for all the users and service providers to identify breaches and adversaries in the service connections for position and location. The swarm density is computed to estimate the breach intensity using the available resources that can be recommended for data protection. The data loss and estimation time are validated for connected services using the condition ({U}_{rq}times pt) and ({U}_{rq}times { s}_{d}) To satisfy successive service responses in this infrastructure, they prevent breach detection. Therefore, the data losses are identified in this article, preventing high service response due to handling sensitive information.
The breach detection and data loss are identified in critical infrastructures based on resource allocation. Service connection with high-level security, which is ensured for a real-time application to achieve high data protection recommendations. The location exploration output is estimated for the connected services and applications employed in the processing system for detecting the vulnerability and data theft in the resources, as illustrated in Fig. 10. This proposed scheme satisfies high service response by computing the estimation time and complexity for the instances. This manuscript combines the reptile exploration and exploitation decision using complexity in these infrastructures to identify the breach at different intervals and prevent data loss. The constraint (DP{left({U}_{rq}right)}_{i} forall Nin {B}_{p}) output helps to achieve high data protection recommendations, whereas a breach in the available resources is processed for service connection until a breach occurs in that platform. Hence, the different resource allocations in the IoT platform are processed to improve data protection and user privacy using RSA to achieve high recommendations and high service response in this proposed scheme.
Protection recommendation.
The processing system in the IoT platform application improves the performance of the connected services based on user requests and service response from the end-users and its associated time at any time interval is depicted in Fig. 11. The post-service access is administered using swarm initialization of the connected real-time applications in the IoT platform. The data loss is identified in the processing system by exchanging information with the user by connecting IoT services for location exploration.
Data loss.
In this proposed scheme, resource management relies on connected services to ensure data authentication and improve the stability of available resources. The service-level fitness is estimated for handling sensitive information and prevents estimation time and complexity. Hence, the data loss is less than the other factors in this proposed scheme. The data loss is identified in a different sequence based on the instance.
The breach/adversaries identification in this critical infrastructure with AI is to improve the estimation time and performance of the real-time application using reptile swarm optimization for the service connection to reduce estimation time. The user request is processed in the IoT platform, and the incremental losses and breaches are identified from different resources in the real-time application, as represented in Fig. 12. In this proposed scheme, the stability of the resources management and allocation for the connected service is analyzed using service-level fitness output is computed for breach detection. From the condition ({U}_{rq}>pt) and (Nleft(Uright)) The estimation time is computed for the service connection and resource management in the processing system to gain a precise service response that augments data protection recommendations. With continuous service connection using RSA, the estimated time for user privacy and data protection in the IoT platform is computed for real-time applications with optimal resource allocation. Based on the location exploration output, the varying swarm density is identified using Eqs. (6), (7), (8), (9), and (10) computations. From this connected service for the active application in the IoT platform, the estimation time is less compared to the other factors.
Estimation time.
This proposed resource management and processing systems in the IoT platform are computed for real-time applications with data loss, and estimation time is calculated depending on security measures provided for the end-users. The swarm density and confronting security for the user information are computed to improve service response using two-factor authentication for user privacy and data protection. The computation of fitness using the proposed scheme is analyzed with user requests and sensitive information to prevent estimation time at the time of service connection in the IoT platform, which is identified using RSA. The time associated with the users and service providers in real-time applications is analyzed. The breach occurrence is determined based on the reptile exploration and exploitation phase’s estimation to improve complexity. Compared to the previous user request processing, the current user request improves the success ratio of service response along with breach detection, preventing data loss. In the proposed scheme for data protection and user privacy through RSA, the estimation time computed for the authentication provided to the available resources achieves less complexity, as represented in Fig. 13.
Complexity.
The reptile search optimization algorithm in the proposed strategy detects breaches better than earlier algorithms. The strategy detects breaches and vulnerabilities quickly using AI-assisted devices and processing systems, minimizing security mishaps compared to previous schemes. Two-factor authentication and elliptic curve cryptography improve privacy protection over earlier approaches. These security measures prevent data breaches and privacy violations by restricting sensitive data access to authorized individuals. The sequential resource allocation method in the suggested system maximizes resource use and avoids waste, improving efficiency over earlier algorithms. Critical infrastructure performs at its peak by dynamically distributing resources in response to user and system demands. A complete critical infrastructure protection method is proposed, including several security mechanisms and optimization techniques.
Unlike prior algorithms, which could concentrate on single security issues, the suggested technique addresses several threats and vulnerabilities, improving security. In comparison, existing algorithms may rely on static security measures or periodic audits, leading to delayed responses to security threats. The suggested strategy uses AI-assisted devices and real-time processing systems to respond dynamically to security threats and incidents, reducing breach detection and mitigation time. The above discussion is summarized in Tables 3 and 4.
The proposed scheme leverages breach detection and protection recommendations by 11.37% and 8.04%, respectively. It reduces the data loss, estimation time, and complexity by 6.58%, 10.9%, and 11.21%, respectively.
The proposed scheme leverages breach detection and protection recommendations by 12.15% and 7.62%, respectively. It reduces the data loss, estimation time, and complexity by 6.13%, 9.35%, and 11.1%, respectively.
The proposed scheme shows an improvement in breach detection compared to other schemes, with an increase of 11.37% to 8.04%. The outcome indicates that the proposed scheme is more effective in detecting breaches in the system. It also demonstrates better performance in protection recommendations, with increased recommendations per access by 11.37% to 8.04%. The result shows that the proposed scheme offers more robust recommendations for protecting the system against potential threats. The proposed scheme reduces data loss by 6.58% to 10.9% compared to other schemes. This implies that the proposed scheme effectively mitigates data loss incidents, enhancing data integrity and security. It also reduces estimation time by 6.58% to 10.9%, indicating improved efficiency in processing requests. This suggests that the proposed scheme offers the fastest response times, enhancing user experience and system performance. The ADP2S reduces complexity by 11.21%, indicating a more streamlined and efficient implementation. The result implies that the proposed scheme offers a more straightforward, manageable solution, reducing resource overhead.
Comparable to Table 3, the recommended breach detection method outperforms others.
The proposed technique improves security breach detection. The suggested strategy works best with more access protection measures and offers actionable network safety suggestions, confirming its strength. The protection recommended system loses less data at 6.13% than other existing approaches, with 12.15%. This illustrates that the proposed technique consistently lowers data loss. Request processing efficiency is shown by the suggested scheme’s shorter estimating time of 9.35 ms. The proposed approach has faster response times than alternative solutions. Like Table 3, the recommended system is more straightforward, making it easier to manage and emphasizes the scheme’s resource efficiency and simplicity by 11.1%.
System failures, poor resource use, and reduced dependability are consequences of the Internet of Things (IoT) systems’ lack of robustness caused by their diverse designs, limited resources, unpredictable network circumstances, and cyber-attack vulnerability. Adaptive defect detection, intelligent resource allocation, and predictive reliability mechanisms are ways AI-assisted devices make the Internet of Things more resilient. One example is defect detection models powered by AI. These models use reinforcement learning methods and deep learning for anomaly detection to find and fix system issues instantly, reducing downtime. Dynamic scheduling and AI-powered federated learning are two examples of adaptive resource allocation approaches that optimize energy consumption, compute resources, and bandwidth in response to current network circumstances, avoiding congestion and decreasing delay. Internet of Things (IoT) devices can now self-heal, reroute data across networks, and adapt performance measurements to changing conditions thanks to AI’s predictive analytics and self-healing capabilities, increasing system dependability. Internet of Things (IoT) systems that incorporate machine learning models for predictive maintenance, artificial intelligence (AI)-driven edge intelligence, and decentralized decision-making are better able to withstand cyber threats, improve operational efficiency, and increase fault tolerance. This makes them more suitable for smart cities, healthcare, and industrial automation.
With the help of reptile-inspired swarm intelligence, the Attuned Data Protection with Privacy Scheme (ADP2S) aims to improve the safety of key infrastructures powered by the Internet of Things (IoT) by detecting and mitigating threats in real-time. When data privacy and protection from cyber threats are paramount, this technology finds widespread use in smart grids, healthcare IoT (e.g., remote patient monitoring), industrial IoT (IIoT) for manufacturing security, and intelligent transportation systems (ITS). Protecting smart grids against cyberattacks and illegal access is one of ADP2S’s primary functions. Protecting private patient information during transmission across the Internet of Medical Things (IoMT) networks is an important part of healthcare IT. In the same way, ADP2S protects IIoT settings’ industrial control systems from cyber invasions and tightens ITS networks’ security to prevent data breaches and illegal vehicle monitoring. Protecting various real-time applications from ever-changing cyber threats, ADP2S offers adaptive security, real-time monitoring, and automatic countermeasures.
This article proposes attuned data protection with a privacy scheme for IoT-aided critical infrastructures. The proposed scheme seeks data protection and user privacy to enhance security and provide better user services. The recommendations are carried out in this protection process using reptile swarm optimization. The swarm is first initialized toward the recommended services for identifying security breaches and data loss. The search and validation are performed considering the reptiles’ exploration patterns. The swarm is initialized based on the service response and allocation to improve authentication integrity. The response to the request is validated as fitness for swarm assignment/ reassignment, depending on the severity of the loss. After the privacy measure, the best-afford reptile is replicated to handle multiple movement patterns. End-to-end two-factor authentication is employed in administering the privacy measure, preventing service connection failures. The fitness estimation is re-instigated to avoid complexity in exploration phases. Therefore, the proposed scheme leverages breach detection and protection recommendations by 11.37% and 8.04%, respectively. It reduces the data loss, estimation time, and complexity by 6.58%, 10.9%, and 11.21%, respectively.
The future scope of the research includes assessing progressed neural network approaches to breach detection, combining blockchain technology into systems for protected data management and verification of transactions, establishing responsive safety protocols that continuously adapt to real-time threat evaluation, expanding research studies to include more critical industries like infrastructure to understand better security issues and possible remedies across domains, and real-world applicability.
Data will be made available on request to the Corresponding Author.
Shi, M., Jiang, R., Hu, X. & Shang, J. A privacy protection method for health care big data management based on risk access control. Health Care Manag. Sci. 23(3), 427–442 (2020).
PubMed MATH Google Scholar
Ferdowsi, A., Saad, W. & Mandayam, N. B. Colonel blotto game for sensor protection in interdependent critical infrastructure. IEEE Internet Things J. 8(4), 2857–2874 (2020).
MATH Google Scholar
Chen, L. et al. An approach of flow compensation incentive based on Q-learning strategy for IoT user privacy protection. AEU Int. J. Electron. Commun. 148, 154172 (2022).
MATH Google Scholar
Baxley, S. M., Bastin, N., Gurkan, D. & Conklin, W. A. Feasibility of critical infrastructure protection using network functions for programmable and decoupled ICS policy enforcement over WAN. Int. J. Crit. Infrastruct. Prot. 39, 100573 (2022).
Google Scholar
Galbusera, L., Cardarilli, M., Lara, M. G. & Giannopoulos, G. Game-based training in critical infrastructure protection and resilience. Int. J. Disast. Risk Reduct. 78, 103109 (2022).
MATH Google Scholar
Li, Y. et al. Joint optimization of structure and protection of interdependent infrastructure networks. Reliab. Eng. Syst. Saf. 218, 108163 (2022).
MATH Google Scholar
Franchina, L. et al. Passive and active training approaches for critical infrastructure protection. Int. J. Disast. Risk Reduct. 63, 102461 (2021).
Google Scholar
Zhang, J., Wang, B., Wang, X. A., Wang, H. & Xiao, S. New group user based privacy preserving cloud auditing protocol. Future Gener. Comput. Syst. 106, 585–594 (2020).
MATH Google Scholar
Al-Kasasbeh, B. Model of the information security protection subsystem operation and method of optimization of its composition. Egypt. Inf. J. 23, 511–516 (2022).
MATH Google Scholar
Ramirez-Gonzalez, M., Sevilla, F. R. S., Korba, P. & Castellanos-Bustamante, R. Convolutional neural nets with hyperparameter optimization and feature importance for power system static security assessment. Electric Power Syst. Res. 211, 108203 (2022).
MATH Google Scholar
Huang, S. Listening to users’ personal privacy concerns. The implication of trust and privacy concerns on the user’s adoption of a MaaS-pilot. Case Stud. Transp. Policy 10(4), 2153–2164 (2022).
MATH Google Scholar
Eldosouky, A., Saad, W. & Mandayam, N. Resilient critical infrastructure: Bayesian network analysis and contract-based optimization. Reliab. Eng. Syst. Saf. 205, 107243 (2021).
MATH Google Scholar
Kaur, H. & Anand, A. Review and analysis of secure energy efficient resource optimization approaches for virtual machine migration in cloud computing. Meas. Sens. 24, 100504 (2022).
MATH Google Scholar
Yin, J., Li, H., Wang, D. & Liu, S. Optimization of rural settlement distributions based on the ecological security pattern: A case study of Da’an City in Jilin Province of China. Chin. Geograph. Sci. 30(5), 824–838 (2020).
MATH Google Scholar
Sascha, K., Thomas, B., Sebastian, G., Ludwig, F. & Günther, F. Optimization of access control policies. J. Inf. Secur. Appl. 70, 03301 (2022).
MATH Google Scholar
Hao, W., Yao, P., Yang, T. & Yang, Q. Industrial cyber-physical system defense resource allocation using distributed anomaly detection. IEEE Internet Things J. 9(22), 22304–22314 (2021).
MATH Google Scholar
Chinnasamy, P. et al. Blockchain 6G-based wireless network security management with optimization using machine learning techniques. Sensors 24(18), 6143 (2024).
PubMed PubMed Central Google Scholar
Oliva, G., Faramondi, L., Setola, R., Tesei, M. & Zio, E. A multi-criteria model for the security assessment of large-infrastructure construction sites. Int. J. Crit. Infrastruct. Protect. 35, 100460 (2021).
MATH Google Scholar
Dong, S. et al. Integrated infrastructure-plan analysis for resilience enhancement of post-hazards access to critical facilities. Cities 117, 103318 (2021).
Google Scholar
Silva, P., Gonçalves, C., Antunes, N., Curado, M. & Walek, B. Privacy risk assessment and privacy-preserving data monitoring. Expert Syst. Appl. 200, 116867 (2022).
Google Scholar
Wang, S., Gu, X., Luan, S. & Zhao, M. Resilience analysis of interdependent critical infrastructure systems considering deep learning and network theory. Int. J. Crit. Infrastruct. Protect. 35, 100459 (2021).
Google Scholar
Rios, E. et al. Security and privacy service level agreement composition for internet of things systems on top of standard controls. Comput. Electr. Eng. 98, 107690 (2022).
Google Scholar
Feizollahibarough, S. & Ashtiani, M. A security-aware virtual machine placement in the cloud using hesitant fuzzy decision-making processes. J. Supercomput. 77(6), 5606–5636 (2021).
MATH Google Scholar
Bing, X. Critical infrastructure protection based on memory-augmented meta-learning framework. Neural Comput. Appl. 32(23), 17197–17208 (2020).
MATH Google Scholar
Chinnasamy, P. et al. Integrating intelligent breach detection system into 6 g enabled smart grid-based cyber physical systems. Wirel. Person. Commun. 8, 1–16 (2024).
Google Scholar
Brignoli, M. A. et al. A distributed security tomography framework to assess the exposure of ICT infrastructures to network threats. J. Inf. Secur. Appl. 59, 102833 (2021).
Google Scholar
Bringhenti, D. et al. Automatic, verifiable and optimized policy-based security enforcement for SDN-aware IoT networks. Comput. Netw. 213, 109123 (2022).
Google Scholar
Miloslavskaya, N. Security zone infrastructure for network security intelligence centers. Proc. Comput. Sci. 169, 51–56 (2020).
Google Scholar
Javanmardi, S., Shojafar, M., Mohammadi, R., Persico, V. & Pescapè, A. S-FoS: A secure workflow scheduling approach for performance optimization in SDN-based IoT-Fog networks. J. Inf. Secur. Appl. 72, 103404 (2023).
Google Scholar
Chinnasamy, P., Deepalakshmi, P., Dutta, A. K., You, J. & Joshi, G. P. Ciphertext-policy attribute-based encryption for cloud storage: Toward data privacy and authentication in AI-enabled IoT system. Mathematics 10(1), 68 (2021).
Google Scholar
Wideł, W., Mukherjee, P. & Ekstedt, M. Security countermeasures selection using the meta attack language and probabilistic attack graphs. IEEE Access 10, 89645–89662 (2022).
MATH Google Scholar
Dedousis, P., Stergiopoulos, G., Arampatzis, G. & Gritzalis, D. A security-aware framework for designing industrial engineering processes. IEEE Access 9, 163065–163085 (2021).
Google Scholar
Download references
The authors extend their appreciation to the Deanship of Scientific Research at Northern Border University, Arar, KSA for funding this research work through the project number ‘‘NBU-FFR-2024-2894-04’’. The authors are thankful to the Deanship of Graduate Studies and Scientific Research at University of Bisha for supporting this work through the Fast-Track Research Support Program. This article has been produced with the financial support of the European Union under the REFRESH – Research Excellence For Region Sustainability and High-tech Industries project number CZ.10.03.01/00/22_003/0000048 via the Operational Programme Just Transition, project TN02000025 National Centre for Energy II and ExPEDite project a Research and Innovation action to support the implementation of the Climate Neutral and Smart Cities Mission project. ExPEDite receives funding from the European Union’s Horizon Mission Programme under grant agreement No. 101139527.
Collage of Information Science and Technology, Zhejiang Shuren University, Hangzhou, 310015, China
Zhenyu Xu, Jinming Wang & Shujuan Feng
Department of Computers and Information Technologies, College of Sciences and Arts Turaif, Northern Border University, Arar, 91431, Saudi Arabia
Salwa Othmen
Department of Computer Science and Artificial Intelligence, College of Computing and Information Technology, University of Bisha, 67714, Bisha, Saudi Arabia
Chahira Lhioui
National Engineering School of Gabes, University of Gabes, Gabès, Tunisia
Aymen Flah
Centre for Research Impact and Outcome, Chitkara University Institute of Engineering and Technology, Chitkara University, Rajpura, Punjab, 140401, India
Aymen Flah
Applied Science Research Center, Applied Science Private University, Amman, 11931, Jordan
Aymen Flah
ENET Centre, VSB-Technical University of Ostrava, Ostrava, Czech Republic
Zdenek Slanina
PubMed Google Scholar
PubMed Google Scholar
PubMed Google Scholar
PubMed Google Scholar
PubMed Google Scholar
PubMed Google Scholar
PubMed Google Scholar
1. Zhenyu Xu: Conceptualization, Methodology. 2. Jinming Wang: Data curation, Writing–original draft, 3. Shujuan Feng: Validation, Writing–review and editing. 4. Salwa Othmen: Writing–original draft, Writing–review and editing. 5. Chahira Lhioui: Writing–review and editing, Supervision. 6. Aymen Flah: Formal Analysis, Validation. 7. Zdenek Slanina: Data curation, Writing–review and editing.
Correspondence to Jinming Wang or Salwa Othmen.
The authors declare no competing interests.
Springer Nature remains neutral with regard to jurisdictional claims in published maps and institutional affiliations.
Open Access This article is licensed under a Creative Commons Attribution-NonCommercial-NoDerivatives 4.0 International License, which permits any non-commercial use, sharing, distribution and reproduction in any medium or format, as long as you give appropriate credit to the original author(s) and the source, provide a link to the Creative Commons licence, and indicate if you modified the licensed material. You do not have permission under this licence to share adapted material derived from this article or parts of it. The images or other third party material in this article are included in the article’s Creative Commons licence, unless indicated otherwise in a credit line to the material. If material is not included in the article’s Creative Commons licence and your intended use is not permitted by statutory regulation or exceeds the permitted use, you will need to obtain permission directly from the copyright holder. To view a copy of this licence, visit http://creativecommons.org/licenses/by-nc-nd/4.0/.
Reprints and permissions
Xu, Z., Wang, J., Feng, S. et al. Optimizing data privacy and security measures for critical infrastructures via IoT based ADP2S technique. Sci Rep 15, 9703 (2025). https://doi.org/10.1038/s41598-025-94824-2
Download citation
Received:
Accepted:
Published:
DOI: https://doi.org/10.1038/s41598-025-94824-2
Anyone you share the following link with will be able to read this content:
Sorry, a shareable link is not currently available for this article.
Provided by the Springer Nature SharedIt content-sharing initiative
Advertisement
© 2025 Springer Nature Limited
Sign up for the Nature Briefing: AI and Robotics newsletter — what matters in AI and robotics research, free to your inbox weekly.


More Stories
Anatomy of a Scam
Climate and Environmental Sustainability Within the IETF and IRTF
From Commitments to Practice: Internet Society’s Priorities for WSIS+20 Implementation